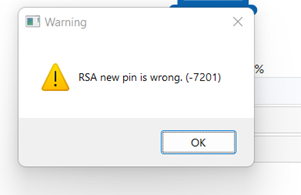
This message is somewhat misleading.
One of our users was attempting to login to the VPN and their Active Directory password had expired.
When they tried to follow the steps to enter their new password they received the above error message.
The root cause was that the new password they were trying to use did not meet the Active Directory password complexity requirements.
So while the error message itself is pretty generic it appears that this is simply what is returned from the back-end Radius server. Not much the Fortigate can do to further interpret the error.
It would be up to the Radius vendor to send a more descriptive error message.